🕵️♂️ Inside the BigONE Breach: $27M Lost in a Silent Backdoor Attack
July 18, 2025
In the early hours of July 16, 2025, the global crypto exchange BigONE fell victim to a highly sophisticated attack that resulted in $27 million in digital assets siphoned from its hot wallets, without a single private key being compromised.
This wasn’t a phishing attack. It wasn’t a wallet-draining exploit.
Instead, it was something far more dangerous: an infrastructure-level compromise that slipped under the radar and rewrote the rules of what a crypto hack can look like.
🧠 A New Class of Exploit
It was confirm that the attackers did not need access to wallet keys or administrative credentials. Instead, they gained entry into BigONE’s backend production systems, likely through a third-party software dependency or misconfigured access point.
Once inside, they modified the logic of the exchange’s internal transaction systems, effectively fooling the platform into processing fraudulent withdrawals as if they were legitimate user requests.
By tampering with risk-control logic, the attackers bypassed withdrawal limits, automated fraud checks, and monitoring systems.
In other words:
They didn't steal the vault. They reprogrammed the vault to hand them the money.
💸 The Stolen Funds
Over the span of several hours, an estimated $27 million was drained from hot wallets spanning multiple chains:
120 BTC
1,272 ETH
8.5 million USDT (TRC-20, ERC-20, BSC, Solana)
1,800 SOL
Additional funds in SHIB, UNI, DOGE, SNT, CELR, and other tokens
Known Attacker Wallets:
Blockchain Address
Ethereum/BSC 0x9Bf7a4dDcA405929dba1FBB136F764F5892A8a7a
Bitcoin bc1qwxm53zya6cuflxhcxy84t4c4wrmgrwqzd07jxm
Tron TKKGH8bwmEEvyp3QkzDCbK61EwCHXdo17c
Solana HSr1FNv266zCnVtUdZhfYrhgWx1a4LNEpMPDymQzPg4R
Lets look through an example through visualisation graph
ETH
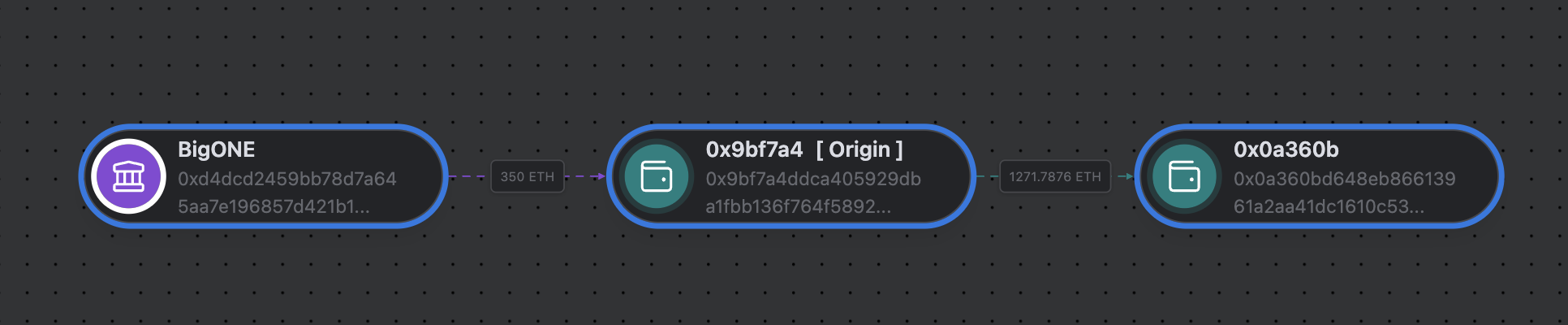
Image captured from the BountyTrack Dashboard (ETH)
⚠️ Silent Signals Ignored?
What makes this attack so alarming is its stealth. The attacker didn’t drain wallets with sudden, suspicious spikes. Instead, they operated under modified logic that made fraudulent withdrawals appear perfectly ordinary within internal systems.
This raises serious questions:
Were there no secondary audit layers to verify transaction legitimacy outside the application logic?
Did the attacker have long-term access, waiting for the perfect moment to strike?
Could this have been an inside job?
BigONE has not disclosed details about how long the attacker had access or which specific systems were compromised, but it’s clear the intrusion was surgical, deliberate, and premeditated.
27 조회