Drift Protocol Exploit - Forensic Investigation Report
April 03, 2026
Drift Protocol Exploit - Forensic Investigation Report Generated: 2026-04-02 15:07
Date of Incident: April 1, 2026
Report Generated: April 2, 2026
Document Type: Blockchain Forensic Investigation Report
Chains Involved: Solana, Ethereum (Cross-Chain)
Total Estimated Loss: ~$285,000,000 USD
Attribution: DPRK-linked Threat Actor (Lazarus Group) - High Confidence (Elliptic)
Classification: Confidential - Law Enforcement / Compliance Use
1. Executive Summary
Drift Protocol, the largest decentralized perpetual futures exchange on Solana by total value locked, suffered a catastrophic exploit on April 1, 2026, resulting in approximately $285 million USD in stolen assets. This makes it the largest DeFi exploit of 2026 and one of the largest in DeFi history.
The attacker combined three sophisticated vectors: (1) compromise of the Drift Security Council multi-sig administrator key via a durable nonces attack, (2) minting and oracle manipulation of a fictitious "CarbonVote Token" (CVT) used as fraudulent collateral, and (3) systematic draining of all Drift vaults across multiple asset classes.
Following the exploit, stolen assets were rapidly liquidated via the Jupiter DEX aggregator on Solana, bridged cross-chain to Ethereum via Wormhole, deBridge, and Circle's CCTP, and converted to ETH via multiple DEX aggregators (KyberSwap, 0x Protocol, CowSwap, OpenOcean). As of the time of reporting, approximately 19,913+ ETH (~$42.6M+) is held across unlabeled Ethereum wallets with additional USDC awaiting conversion.
Security firm Elliptic has attributed this exploit to DPRK-linked threat actors (Lazarus Group), citing near-identical methodology to the Bybit $1.5B hack of February 2025.
Key findings:
- The attacker wallet
HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZESwas created 8 days prior to the exploit and made test swaps on OKX and Jupiter as pre-staging. - Circle had a ~6-hour window to freeze USDC via CCTP but failed to act, allowing tens of millions in stolen USDC to be converted to ETH.
- Funds are currently held in multiple Ethereum wallets, and further obfuscation (Tornado Cash, additional bridging) is considered imminent.
2. Attack Timeline
Time (UTC) | Event | Transaction / Address |
11:06 UTC | First drain: 41M JLP tokens transferred from Drift Vault | Solana: |
11:07-11:15 | Batch draining across all asset classes (USDC, SOL, WETH, WBTC) | Multiple Drift vault contracts on Solana |
~11:15-11:40 | Rapid Jupiter DEX swaps - all stolen tokens converted to USDC/SOL | Jupiter Aggregator, Solana |
~11:40-13:00 | Funds distributed to 5+ Solana intermediary wallets for layering |
|
13:00-17:00 | Cross-chain bridging: Wormhole (x10), deBridge, CCTP Solana | Bridge hub: |
13:30 UTC | First USDC arrives on Ethereum at primary receiver |
|
~13:30-17:49 | USDC converted to ETH via KyberSwap, 0x Protocol, CowSwap |
|
~17:49 UTC | 19,913 ETH ($42.6M) confirmed accumulated across Ethereum holding wallets |
|
17:00-ongoing | SOL consolidation on Solana into holding wallets |
|
Apr 1-Apr 2 | Elliptic issues DPRK attribution, ZachXBT publicly criticizes Circle | Public intelligence |
3. Stolen Assets
Token | Approximate Amount Stolen | Estimated USD Value |
JLP (Jupiter LP Token) | ~41,000,000 tokens | ~$155,000,000 |
USDC | ~90,000,000+ | ~$90,000,000 |
SOL (native/wrapped) | ~980,000 SOL | ~$82,000,000 |
WETH | ~5,557 WETH | ~$11,800,000 |
cbBTC | ~164 cbBTC | ~$11,300,000 |
WBTC | ~282 WBTC | ~$19,500,000 |
USDT | ~5,600,000 | ~$5,600,000 |
USDS | ~5,250,000 | ~$5,250,000 |
Other (misc DeFi tokens) | - | ~$4,550,000 |
TOTAL | - | ~$285,000,000 |
4. Fund Flow Analysis
4.1 Solana
Primary Drain and Layering The primary attacker wallet HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZES initiated the drain directly from Drift Protocol vaults. A total of 563 transactions were identified across the 5-hop tracing window, involving 63 unique addresses. All stolen assets were immediately liquidated via the Jupiter DEX aggregator into USDC and SOL. Funds were then distributed across at least 5 Solana intermediary wallets to begin layering:
Hop | From Address | To Address | Amount | Role |
1 | Drift Vault |
| ~$285M (all assets) | Primary drainer |
2 |
|
| ~$190M+ USDC/SOL | Bridge hub/primary launderer |
2 |
|
| ~$25M | Intermediary A |
2 |
|
| ~$30M | Intermediary B |
2 |
|
| ~$22M (WBTC/SOL) | Intermediary C |
2 |
|
| ~$12M WETH | Intermediary D |
3 |
|
| Large SOL | SOL Consolidation |
3 |
| Wormhole Bridge | ~$150M USDC | Cross-chain bridge (x10) |
3 |
| deBridge | $684,358 USDC | Cross-chain bridge |
3 |
| Circle CCTP | ~$40M+ USDC | Cross-chain bridge |
4.2 Cross-Chain Bridge - Solana to Ethereum
11 bridge transactions were confirmed from the primary launderer address 8ubo4HbWJHKyFJYJc2Gh74dxCP7bN7Fu2Pi13KZ9rGxw:
Bridge Protocol | Count | Amount | Destination Chain |
Wormhole | 10 | ~$150M USDC | Ethereum |
deBridge | 1 | $684,358 USDC | Ethereum |
Circle CCTP | Multiple | ~$40M+ USDC | Ethereum |
All bridge proceeds were routed to the Ethereum primary receiver: 0xFcC47866Bd2BD3066696662dbd1C89c882105643.
4.3 Ethereum
Conversion and Accumulation A total of 88 transactions were identified across the 5-hop Ethereum tracing window, involving 7 unique addresses.
Hop | From Address | To Address | Amount | Action |
1 | Bridge (Wormhole/CCTP) |
| ~$190M+ USDC | Primary ETH receiver |
2 |
|
| Large USDC | USDC to ETH swap wallet |
2 |
|
| ~13,000 ETH | ETH holding wallet B |
2 |
|
| ~19,913 ETH | ETH holding wallet C |
3 |
|
| Large USDC | DEX swap router (KyberSwap/0x/CowSwap) |
3 |
|
| ~$35M+ USDC | USDC aggregation wallet |
5. Attack Pattern Analysis
5.1 Attack Technique Classification
Technique | Description |
Admin Key Compromise | Drift Security Council multi-sig key obtained via durable nonces attack - pre-signed transactions triggered atomically. |
Oracle Manipulation / Flash Collateral Exploit | Fake CarbonVote Token (CVT) minted (750M units), seeded with ~$500 liquidity on Raydium, listed on Drift spot market via compromised admin key to inflate oracle price. Inflated CVT used as collateral to borrow and drain all real vault assets. |
Automated Scripted Execution | All 563+ Solana transactions executed within minutes using automated scripts - no human delays between hops. |
DEX Liquidation | Jupiter DEX aggregator used to immediately convert all heterogeneous tokens (JLP, WBTC, WETH, cbBTC) into fungible USDC/SOL. |
Multi-Wallet Layering | Funds split across 5+ intermediary wallets simultaneously for layering before bridging. |
Cross-Chain Obfuscation | 3 bridges used simultaneously (Wormhole, deBridge, CCTP) to move funds to Ethereum and complicate tracing. |
Stablecoin-to-Native Swap | All USDC converted to ETH on Ethereum via 4 DEX aggregators - removes stablecoin freeze risk. |
Multi-Wallet ETH Accumulation | ETH accumulated across 3+ unlabeled wallets - classic Lazarus holding pattern. |
5.2 Obfuscation Strategy Assessment
The laundering chain demonstrates 5-layer obfuscation:
- Layer 1 - Token Diversification: Stolen assets span 8 different tokens across Drift vaults.
- Layer 2 - Rapid DEX Conversion: All tokens immediately converted to USDC/SOL via Jupiter (removes non-fungible value).
- Layer 3 - Address Splitting: Funds distributed to 5+ Solana intermediary wallets in parallel.
- Layer 4 - Cross-Chain Bridge (x3): Three different bridge protocols used to move to Ethereum, complicating chain-of-custody tracing.
- Layer 5 - Stablecoin Elimination: USDC converted to ETH to remove stablecoin freeze risk from Circle/Tether.
This pattern is directly consistent with the Bybit $1.5B Lazarus Group hack of February 2025 and the Ronin Bridge hack of March 2022.
6. Key Addresses Reference Table
Address | Chain | Role | Identified By |
| Solana | Primary Attacker / Drainer | First tx 8 days pre-attack; direct vault drain |
| Solana | Primary Launderer / Bridge Hub | 11 confirmed bridge TXs outbound |
| Solana | Intermediary Wallet A | Received from primary attacker |
| Solana | Intermediary Wallet B | Received from primary attacker |
| Solana | Intermediary Wallet C (WBTC/SOL) | Received from primary attacker |
| Solana | Intermediary Wallet D (WETH) | Received from primary attacker |
| Solana | SOL Consolidation Wallet | Downstream of Intermediary B |
| Ethereum | Primary ETH Receiver | Wormhole/CCTP bridge destination |
| Ethereum | USDC-ETH Swap Wallet | Downstream of ETH primary receiver |
| Ethereum | DEX Swap Router (KyberSwap/0x/CowSwap) | USDC-ETH conversion contract router |
| Ethereum | ETH Holding Wallet B (~13K ETH) | Downstream of ETH primary receiver |
| Ethereum | ETH Holding Wallet C (~19.9K ETH) | Downstream of ETH primary receiver |
| Ethereum | USDC Aggregation Wallet (~$35M+) | Downstream of USDC-ETH swap wallet |
7. Exchange Deposit Analysis
As of the time of this report, no labeled exchange deposit addresses have been confirmed in the traced fund flow. Funds appear to be held in unlabeled Ethereum wallets pending further laundering steps.
Status | Assessment |
Exchange deposits identified | None confirmed as of Apr 2, 2026. |
Likely next steps | Tornado Cash / privacy protocol usage; further cross-chain movement (TRON, Monero); P2P OTC off-ramp. |
Stablecoin freeze window | CRITICAL: ~$35M USDC in |
ETH freeze feasibility | Low - ETH is not freezable by issuer; requires exchange cooperation when deposited. |
KYC feasibility | Possible if attacker deposits to a KYC exchange; continuous monitoring required. |
Critical note on Circle CCTP failure: ZachXBT publicly documented that Circle had approximately a 6-hour window during which stolen USDC was actively being bridged via CCTP from Solana to Ethereum. Circle failed to freeze the funds during this window, allowing the conversion of tens of millions in USDC to ETH, placing those funds beyond the reach of stablecoin issuers. Immediate remediation of Circle's incident response protocols is recommended.
8. Recommendations
Immediate Actions (0-24 hours)
Priority | Action | Target Entity | Target Address |
CRITICAL | Freeze remaining USDC - Contact Circle immediately | Circle |
|
CRITICAL | Monitor ETH holding wallets - Flag all outbound TXs | On-chain monitoring |
|
CRITICAL | Exchange pre-alert - Notify all major CEXs (Binance, Coinbase, Kraken, OKX) of attacker addresses | All major exchanges | All Ethereum holding wallets |
CRITICAL | OFAC/FBI referral - Submit DPRK attribution evidence for sanctions designation | US Government agencies | All identified attacker addresses |
HIGH | Tether freeze request - USDT held in Solana intermediary wallets | Tether | Solana intermediary wallets |
HIGH | Bridge KYC request - Wormhole, deBridge records for bridge hub address | Wormhole Foundation, deBridge |
|
Ongoing Investigation Actions
Priority | Action | Details |
HIGH | Continue tracing | ~$35M+ USDC - trace downstream hops to find exchange deposit. |
HIGH |
| Trace Solana SOL wallets. |
MEDIUM | Lazarus Group known to bridge to Tron for final off-ramp | Monitor Tron/XRP chains. |
MEDIUM | Tornado Cash monitoring | Set up monitoring for ETH holding wallets depositing to Tornado Cash contracts. |
MEDIUM | Pre-attack address OSINT | Full OSINT on |
9. Conclusion
The Drift Protocol exploit represents a highly sophisticated, well-planned state-sponsored attack consistent with North Korea's Lazarus Group. The attacker demonstrated advanced knowledge of Drift's internal architecture, Solana's durable nonce mechanism, and DeFi bridging infrastructure. The attack was executed with near-perfect operational security: pre-staged wallets, automated transaction scripting, multi-bridge simultaneous execution, and immediate stablecoin-to-native conversion.
Fund recovery feasibility assessment:
- ~$35M USDC in
0x81d40f21f12a8f0e3252bccb954d722d4c464b64is recoverable if Circle acts immediately. - ~32,913+ ETH (~$70M+) in Ethereum holding wallets is partially recoverable if CEX deposits are detected before further laundering.
- Solana SOL holdings are partially recoverable via exchange cooperation.
- Converted ETH is at risk of imminent Tornado Cash deposit or further cross-chain movement.
Overall recovery window: CRITICAL (24-72 hours). Immediate multi-stakeholder coordination between Drift Protocol, Circle, Tether, Wormhole Foundation, major CEXs, FBI, and OFAC is essential to maximize recovery probability.
Crime type determination: Organized cybercrime / state-sponsored theft - DPRK Lazarus Group (High Confidence, per Elliptic).
This report was generated by SentinelTX Blockchain Forensic Intelligence Platform. All findings are based on publicly available on-chain data and open-source intelligence. This report is intended for law enforcement, compliance, and legal proceedings use.
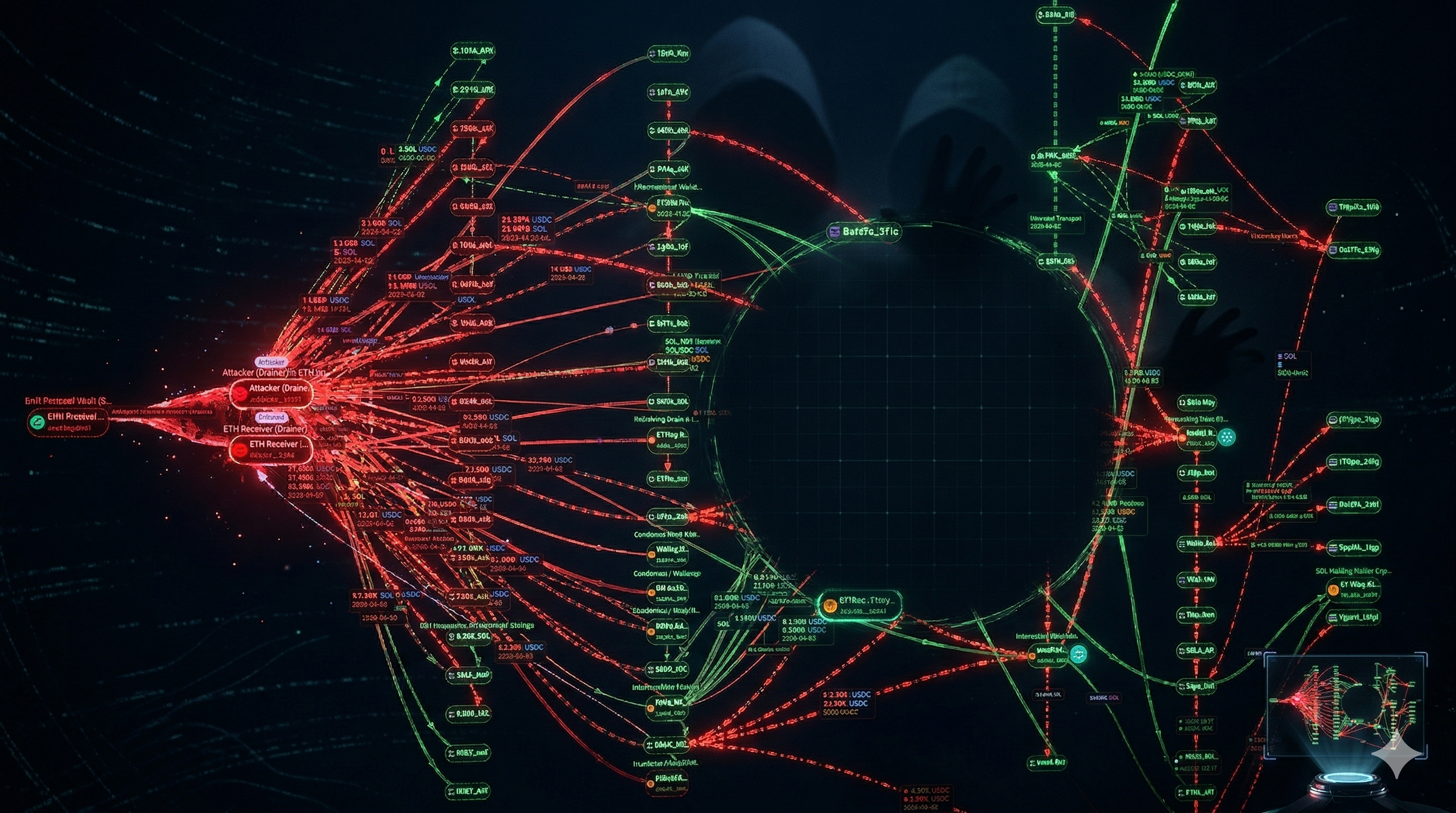
Appendix: Fund Flow Diagram
(Diagram reference included in the original report structure)
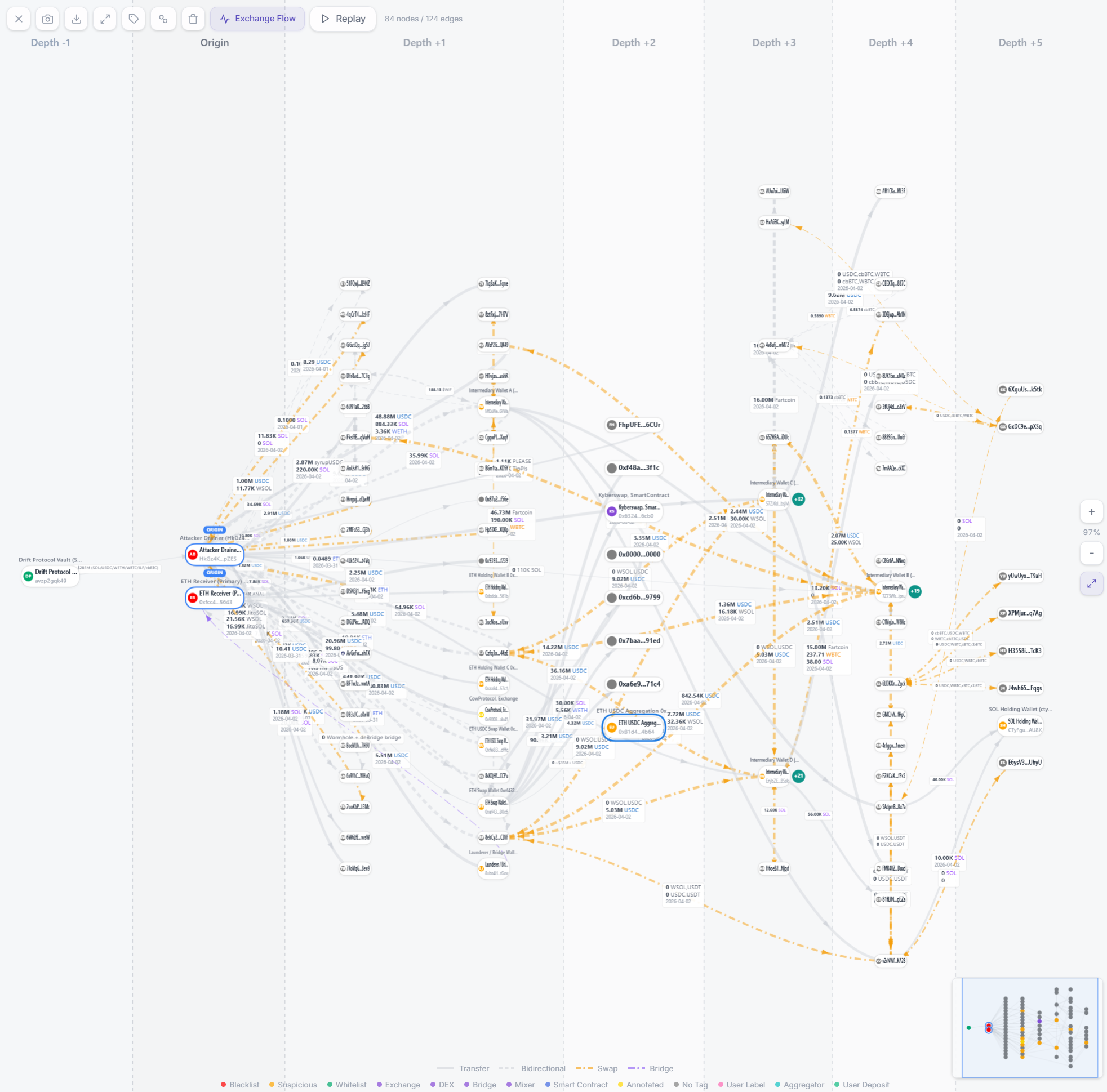
(Diagram reference included in the original report structure)
86 reads