Aethir (ATH) Bridge Exploit: Technical Post-Mortem
April 12, 2026
Introduction: The Principle of Transparency and Community Trust
Dear Aethir Community and Partners,
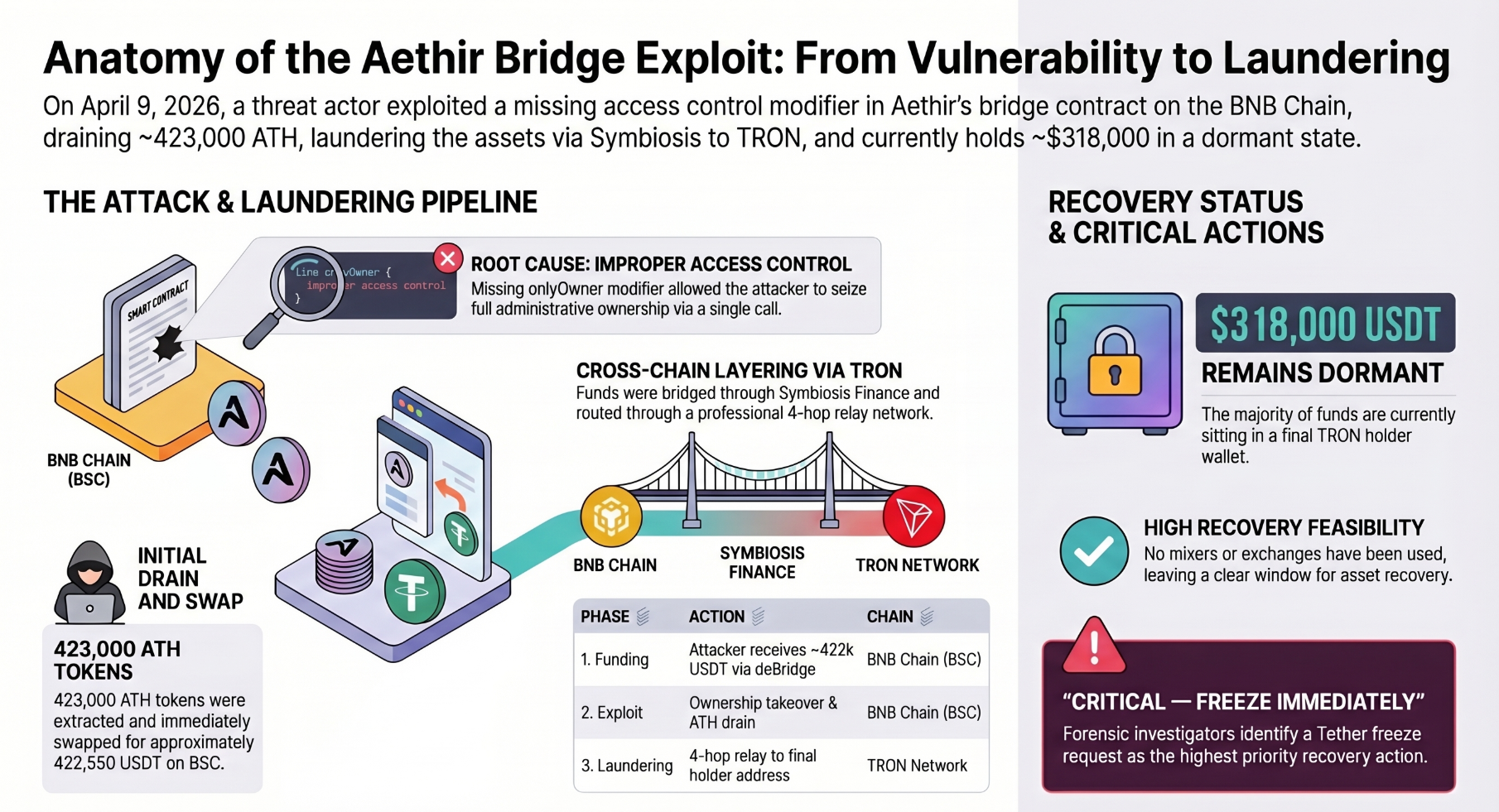
As a global leader in decentralized GPU cloud computing and AI infrastructure, Aethir bears the responsibility of maintaining the highest standards of security and transparency alongside our technological innovations. On April 9, 2026, a malicious exploit attempt occurred on the AethirOFTAdapter contract, one of Aethir's cross-chain bridge infrastructures.
Upon detecting the anomaly, our security team immediately isolated the compromised contract from the main network, successfully preventing any further damage. While the total exploited amount was approximately $400,000, our rapid response ensured that direct financial losses to individual users were strictly capped at under $90,000. We can confirm that the total supply of ATH tokens on the Ethereum mainnet and our core infrastructure (such as the ETH-ARB Squid bridge) remain completely unaffected and fully operational.
Aethir places the utmost priority on our relationship with the community. Through this post, we are transparently sharing all technical details regarding how the incident occurred, the ongoing tracking of funds, our compensation plan for affected users, and the enhanced security measures we are implementing.
Understanding the Aethir Ecosystem and Cross-Chain Bridge Architecture
To understand this incident, it is essential to understand the nature of Aethir's decentralized infrastructure and the role of cross-chain bridges. Aethir is a massive DePIN ecosystem that connects over 435,000 high-performance GPUs (such as NVIDIA H100s) distributed across 93 countries, providing compute power for AI training and cloud gaming. Through this network, Aethir has experienced explosive growth, surpassing $141 million in Annual Recurring Revenue (ARR).
The core asset unifying these global hardware resources and distributing rewards is the ATH token. Originally deployed on the Ethereum mainnet, the ATH token required cross-chain expansion to networks like BNB Chain (BSC) and Arbitrum to reduce transaction fees and scale the ecosystem.
For this purpose, Aethir adopted LayerZero's OFT (Omnichain Fungible Token) framework, a global standard for cross-chain interoperability. Standard OFT architecture uses a "Burn-and-Mint" mechanism. However, for existing ERC-20 tokens already deployed on Ethereum, a wrapper contract called an OFTAdapter is used to bridge assets by locking and unlocking tokens.
Consequently, the AethirOFTAdapter on the BSC network served as a central vault holding a significant reserve of ATH liquidity deposited by users for cross-chain transfers. This structural characteristic made it a prime target for the attackers.
Technical Root Cause: Smart Contract Access Control Failure
On April 9, 2026, the attacker did not utilize complex techniques like oracle price manipulation or flash loans. Instead, they exploited one of the most fundamental and critical flaws in smart contract security: an "Improper Access Control" (CWE-284) vulnerability.
The core of the attack vector lay in the transferOwnership() function, which modifies administrator privileges. Typically, such functions must be strictly protected by access modifiers like onlyOwner to ensure they can only be called by the legitimate current owner.
However, the AethirOFTAdapter deployed on BSC either lacked this essential verification logic or was designed in a way that could be maliciously bypassed. This allowed the attacker's wallet (0xd5fa8ac45d6a0984d14f3b301b18910948deb11a), an Externally Owned Account (EOA) with no prior authorization, to execute a direct external call to the function.
By acquiring the official "Owner" status of the contract in a single transaction, the attacker freely invoked liquidity withdrawal functions restricted to administrators, transferring approximately 423,000 ATH from the adapter to their own wallet. In architectures like the LayerZero OFT adapter, where massive value is protected by a single ownership key, bypassing ownership equates to gaining full access to all funds within the contract.
Exploit Timeline and Cross-Chain Fund Tracking
Thanks to the transparency of the blockchain, all attacker activities were permanently recorded on the distributed ledger. Professional forensic investigations confirmed that this attack was a highly sophisticated, multi-phase operation.
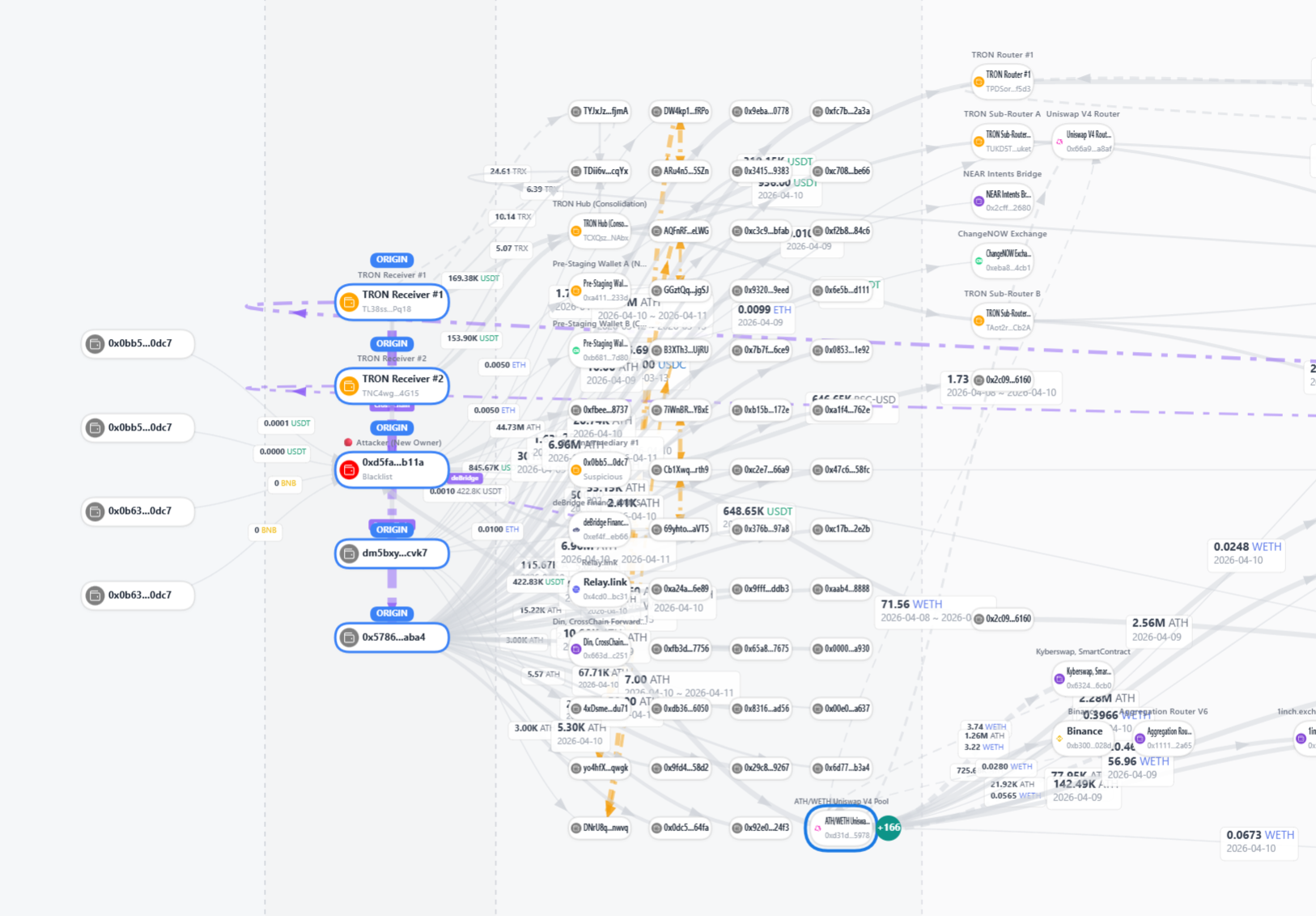
Phase 1: Pre-Funding and Preparation (via deBridge)
Just hours before the attack, the attacker received approximately 422,833 USDT across four batch transactions via the deBridge CrossChain Forwarder Proxy (0x663dc15d3c1ac63ff12e45ab68fea3f0a883c251) on the BNB Chain. This amount almost exactly matches the final stolen funds (~422,550 USDT). This indicates a pre-planned operation where the attacker secured seed capital in advance after analyzing the vulnerability.
Receiving Wallet (Attacker) | Funding Route (via deBridge Proxy) | Amount Funded | Transaction (April 9, 2026) |
0xd5fa8a...deb11a | 0x555c3b...e07c35b | 184,256.47 USDT | 0x1e13c1...21df |
0xd5fa8a...deb11a | 0x555c3b...e07c35b | 108,450.18 USDT | 0xdca5e9...741e |
0xd5fa8a...deb11a | 0x555c3b...e07c35b | 108,425.82 USDT | 0xfe20b6...e302 |
0xd5fa8a...deb11a | 0x555c3b...e07c35b | 21,701.23 USDT | 0xc8a9d2...80ab |
Total | ~422,833 USDT |
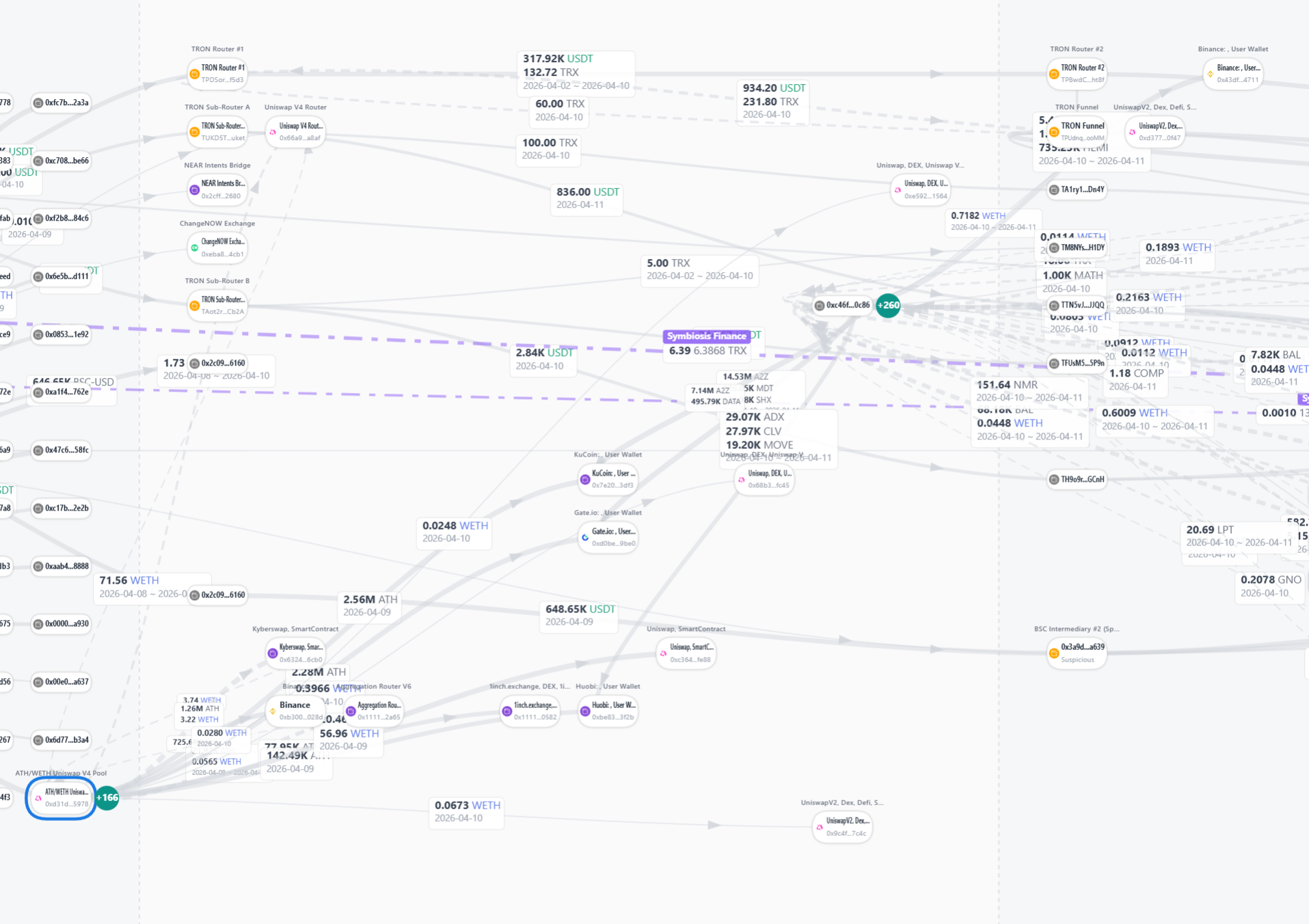
Phase 2: Execution and Layering on BSC
On April 9, after seizing ownership, the attacker withdrew ~423,000 ATH and immediately swapped it for 422,550.71 USDT. To evade tracking, the attacker layered the funds by dispersing them across multiple intermediary wallets on the BSC network. The funds were split into two main branches: ~324,000 USDT to the first intermediary (0x0bb5ec...b0dc7) and ~202,000 USDT to the second intermediary (0x3a9d44...a639). Notably, the second wallet employed anti-forensic patterns by dividing the funds into six smaller batches, including 50,000 USDT increments.
Phase 3: Escape to TRON via Symbiosis Finance
The fragmented USDT on the BSC chain was then bridged to the TRON network using Symbiosis Finance (0x44487a445a7595446309464a82244b4bd4e325d5), a non-custodial cross-chain bridge with no KYC requirements. Using deBridge for funding and Symbiosis for escaping was a strategic choice to obscure on-chain correlation. The bridged funds arrived in two TRON receiving wallets, holding ~169k USDT and ~153k USDT, respectively.
Phase 4: TRON Routing Network and Final Consolidation
Upon arriving on TRON, the funds were consolidated in a central hub (TCXQszGad9YRGgnPefKfnTc8wrTHxXNAbx) and passed through a complex 4-hop routing chain (Router #1 -> #2 -> #3 -> Funnel) designed to completely obfuscate the source of the funds. As of April 11, approximately 318,000 USDT has consolidated in a single dormant TRON address (TKX4y5jbKc43x8KkSBSiEF5sJWU6e2ZGHA).
Asset Tracking Status | Current Balance | Network | Status & Risk Level |
Initial Drained Asset (ATH) | 423,000 ATH | BSC | Swapped to USDT and routed out |
Final Consolidated Funds (USDT) | ~318,000 USDT | TRON | Dormant (TKX4...ZGHA) / Freeze Window Open |
Residual Funds | ~2,000 USDT | TRON | Scattered across sub-router wallets |
Residual Dust | ~1,065 USDT | BSC / ETH | Left in the attacker's initial wallets |
Threat Intelligence: Pre-Staged Professional Criminal Infrastructure
The most critical forensic finding is that the TRON network infrastructure used to launder the funds had been operational long before the hack occurred.
The TRON sub-router wallet (TAot2rJwZkVkCvkoqPfojgfUfrf6R2Cb2A) had been acting as a professional USDT relay service since March 30, 2026—10 days prior to the Aethir exploit. Between March 30 and April 9, this wallet continuously received over $300,000 in USDT from multiple feeder wallets and relayed them to a downstream accumulator.
Pre-Hack TRON Feeder Wallets | Activity (Late March ~ Early April 2026) |
TVxARF4Vvi87d6YSnTsXSxWaDPoV3najDo | Sent 88,426 USDT (Largest single feeder) |
TUKda694TPAXXtVHmKYe2KR9LZjQuHqCQX | Sent 42,348 USDT |
TCXWXSHA4bbA5iNLLwCzKFyDrQFiwHqYRz | Sent 31,052 USDT and 7,225 USDT |
TQ9YsUXttHatVuMVar3QiiRCMV77777777 | Sent >$30,000 (Vanity address pattern) |
TSWsmHau7c6jDNk3izbYoP7ciwtTqR2QmC | Sent >38,000 USDT across multiple tranches |
This infrastructure also displayed highly automated operational patterns, such as sending 0.1 TRX daily to cover gas fees. This strongly suggests the attacker utilized Crime-as-a-Service (CaaS) to rent a professional cybercriminal cartel's money-laundering network, or that they are part of an organized syndicate themselves. TRON's fast speeds and low fees make it a frequent channel for illicit laundering globally.
Fund Recovery Strategy and the Critical Role of Tether (USDT) Freezes
Although highly sophisticated laundering techniques were employed, the fact that approximately 318,000 USDT remains dormant in a single TRON address without passing through a mixer provides a crucial opportunity for recovery.
Unlike fully decentralized cryptocurrencies, USDT is centrally issued by Tether Ltd. Tether has the authority to permanently blacklist specific wallet addresses involved in illicit activities, freezing the movement of tokens at the smart contract level upon legitimate requests from international law enforcement.
Once a freeze is approved, Tether can initiate a "Burn and Reissue" mechanism, rendering the hacker's USDT useless and reissuing the equivalent amount to a recovery wallet for victim compensation. Tether has a strong track record of this, having frozen over $4.2 billion in USDT linked to scams and illicit activities.
Aethir is currently working closely with global security partners and law enforcement to submit an urgent Tether (USDT) freeze request for the targeted TRON addresses, specifically TKX4y5jbKc43x8KkSBSiEF5sJWU6e2ZGHA and TCXQszGad9YRGgnPefKfnTc8wrTHxXNAbx. Forensic reports estimate a 70-80% recovery probability if the funds do not move to an OTC desk.
Aethir's Post-Incident Response and User Compensation Plan
Aethir is taking decisive actions to protect the trust of our ecosystem participants and users:
- Global CEX Coordination: Immediately following the incident, Aethir established hotlines with top-tier exchanges including Binance, Upbit, Bithumb, and HTX. Over 20 identified hacker and intermediary wallets have been added to exchange blacklists to completely block cash-out (off-ramp) attempts.
- Security Architecture Overhaul: The compromised AethirOFTAdapter contract has been permanently isolated. We are conducting an in-depth audit of our entire cross-chain bridge architecture and multi-sig systems through top-tier external blockchain security firms to implement a multi-layered defense mechanism.
- Full User Compensation Plan: Direct financial losses to individual users have been confirmed to be under $90,000. The Aethir Foundation prioritizes user protection and possesses the financial stability (over $141 million in ARR and a $50 million ecosystem fund) to fully cover these losses.
A detailed compensation plan and claims process will be transparently announced next week via Aethir's official Discord community and blog. Please be aware of phishing scams and only verify the compensation process through official Aethir channels.
We will use this incident as a profound learning opportunity to drastically fortify our security infrastructure. Thank you to our community for your continued trust and patience.
APPENDIX: FUNDFLOW CHART
deBridge Forwarder Proxy (0x663dc15d3c1ac63ff12e45ab68fea3f0a883c251)
│
▼ (4 Batched TXs: ~422,833 USDT)
Attacker EOA (0xd5fa8ac45d6a0984d14f3b301b18910948deb11a)
│
▼ (Drains ~423,000 ATH, Swaps to ~422,550 USDT)
BSC Intermediaries (0x0bb5ec08931fdae1587f2b4c47185343831b0dc7 & others)
│
▼ (Layering & Batch Splitting)
Symbiosis Finance Bridge (0x44487a445a7595446309464a82244b4bd4e325d5)
│
▼ (Cross-Chain Transfer)
TRON Receivers (TL38ssgWktRRfhdjGEyfVkPD8CdP2UPq18 & TNC4wgK518RZdZVa6NPZLnqy6FEswA4G15)
│
▼
Consolidation Hub (TCXQszGad9YRGgnPefKfnTc8wrTHxXNAbx)
│
▼ (4-Hop Relay Chain)
Router #1 (TPDSor5YhDzVQDFBTont7SxgnLJCiff5d3)
│
▼
Router #2 (TPBwdCFVwbFouwftG5SMR5Fw69F3EHht8f)
│
▼
Router #3 (TRWDAUTJuRe6rSqQwx9cqS3cJzuUF2K5yP)
│
▼
Funnel (TPUdnqvwhjyYd3HcDGgxsHUHBHYDVVooMM)
│
▼
Final Dormant Holding Address (~318,000 USDT)
(TKX4y5jbKc43x8KkSBSiEF5sJWU6e2ZGHA)
From Depth -1 to Depth 2
Depth 2
5 reads